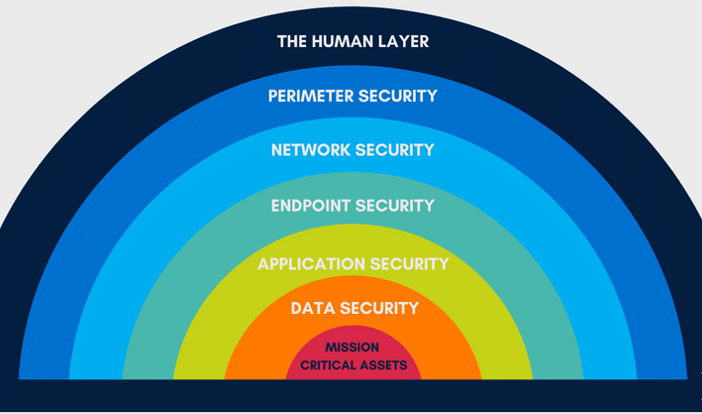
Layered security isn’t a new concept. It’s been around since as long as humans have tried to keep things safe. From a castle with a moat and high walls and guards, to modern day banks with cameras and vaults. Layered security is a classic concept. When we talk about information security, it is always in the context of layered security. For those of you who were not morning people in school, it’s like having only a single alarm set, with no snooze button.
1. Human Layer: Training
We really can’t say enough about User training and security awareness. Verizon releases an annual Data Breach report, and it spells out that 94% of malware is delivered via email. Phishing attacks account for more than 80% of reported security incidents. These same kinds of studies also tell us that the Human firewall is always the weakest link in the security chain.
Greg Keller says the two greatest concerns are number one ‘Are my employees trained regularly to detect, second guess, and report a phishing email or website?’ and number two “Are all of my corporate resources that allow authentication protected with multi-factor authentication’.
Start there, and rinse/repeat until your employees are trained and protected.
Most organizations don’t realize how vulnerable they really are to attack. Some of the easiest fixes are as simple as having a properly configured business class firewall, ensuring good patch management for your systems, and enabling good security policies.
That’s It. Very simple changes can remove three quarters of these low-skill vulnerabilities.
2. Perimeter: Firewalls, Spamfilter, Intrusion Detection/Prevention
Think of the perimeter as the outermost wall. This can be a fence around your company’s property. Or a fence around your email. Or your internal network.
The perimeter layer stops most attackers. It stops the spam, the petty thief, the automatic scanning tools run by anonymous curious cats. The perimeter is both the most effective layer from a numbers standpoint, but often the worst configured, where a single mistake can allow anything in. Like a gate left open.
3. Network: Secure Design & Topology, VLANs, Multi-Layer Firewalls/Switches
Now, I want you to picture that someone has come into that gate left open. They climbed over the fence. Or they found the front door unlocked. Whatever the method, they just walked in. When my wife complains about her mother in law, I have to tell her that it’s too late. She married me and now my mother, is also her mother. So now that they are in, the goal is to slow them down, or at least stop them from reaching their target. Like a maze.
Secure design is about ensuring that even if someone gets into your network, they only have limited ways of traveling through it.
4. Endpoint: Anti-virus, Software Firewalls, Breach Detection Agents
This is the lock on each deposit box in a back. At this point they’re past the locks, the cameras, the guard, and are actively in the building trying to find something juicy on the endpoint. The endpoint can be a computer, or a server, or even a phone. Antivirus really rules the market here when it comes to endpoint security. They come in many different flavors such as signature based, behavioral based, heuristic, etc.
But chances are that everyone has one of these products installed. And if you know all these products, you can bet that the bad guys do as well. It’s helpful, like a firewall it will stop most attackers… but not all.
5. Application: Patching, updates
If you do not use Diamond IT, it is beyond essential that your IT team uses some kind of tool to ensure patching is done in a timely and comprehensive manner. One of our internal reports showed 12,000 found vulnerabilities for our customers last month.
If your organization has a CISO, this should be at the top of their list to review every month.
6. Data: Encryption at rest and in motion.
Needless to say, encryption and data security is about securing the data itself. So once they are in the deposit box and they find the treasure map they still can’t read it. The laptop hard drive can’t be used. The email you sent to HR, can’t be opened and isn’t legible. That’s what encryption does for us. It maintains confidentiality and integrity of the data.
7. Mission Critical: Backups, Response and Recovery Plans
In our next post, we will provide a deep dive into incident response planning. Stay tuned! In the meantime, learn more about our IT services.